MANUAL JAILBREAK: Enable ADB and DevTools in a data partition image
by Luxferre
Unfortunately not all KaiOS devices have the same possibilities. To help users better understand which installation method is more suitable for their device, we have classified KaiOS devices based on two difficulty levels: Debug-enabled and locked.
Debug-enabled, for these devices it is sufficient to type one or two codes to enable USB debugging (Nokia phones, Energizer, Positivo, etc...), you can apply the natural sideload methods and the official jailbreak guide for these devices without any problem;
Locked devices have no working codes because blocked by the OEM by default. All devices with a relative loader can be used to flash in EDL mode a data partition image (CAT B35 and Jio Phone first of all).
If your device is locked and without working codes or ADB and DevTools access, this method is for you.
In this guide we need to do is to enable the "developer menu" and ADB if unauthorized/disabled on the device. This should ensure the normal functioning of KaiOS according to the nature of Firefox OS, and without losing updates. The basic requirements are:
Your PC with ADB installed and configured;
A way to get your userdata.img file from your phone (for example using EDL.PY and the correct firehose for your device);
An Hex editor, like wxHexEditor, to read and manage the usedata.img file;
A root shell on your PC.
NOTE: to activate ADB on your device in some cases it is not enough to patch only the data partition. In fact the drivers for ADB are contained within the firmware. This could involve adding another partition to be modified, but more often adding the ADB public key is enough.
Before starting
Using EDL.PY for your device (for example your-firehose-x0000b.mbn) you must know how to:
First get the partition table layout with -printgpt option:
python3 edl.py -loader your-firehose-x0000b.mbn -printgpt
Backup any partition from the device with -r [partname] [filename] option. For instance (in our case we need to work on "userdata"):
python3 edl.py -loader your-firehose-x0000b.mbn -r recovery userdata.img
To erase the partition, supply the -e [partname] option:
python3 edl.py -loader your-firehose-x0000b.mbn -e userdata
To flash the new partition image, supply the -w [partname] [filename] option:
python3 edl.py -loader your-firehose-x0000b.mbn -w userdata userdata.img
Enable the developer menu
The simplest way to do this is to patch the runtime setting developer.menu.enabled in the userdata partition image. The only problem is that, unlike system partition, this setting in userdata resides in some kind of database. So, to avoid unpacking, searching, patching and repacking, we can resort to dirty direct patching of a dumped userdata partition:
1. Open the userdata partition dump in a hex editor like wxHexEditor;
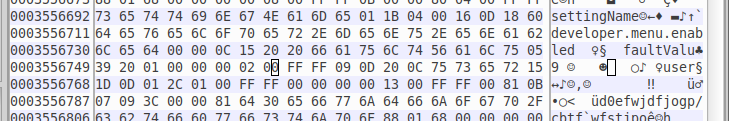
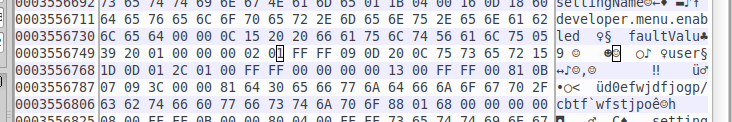
2. Look for the developer.menu.enabled string in the dump;
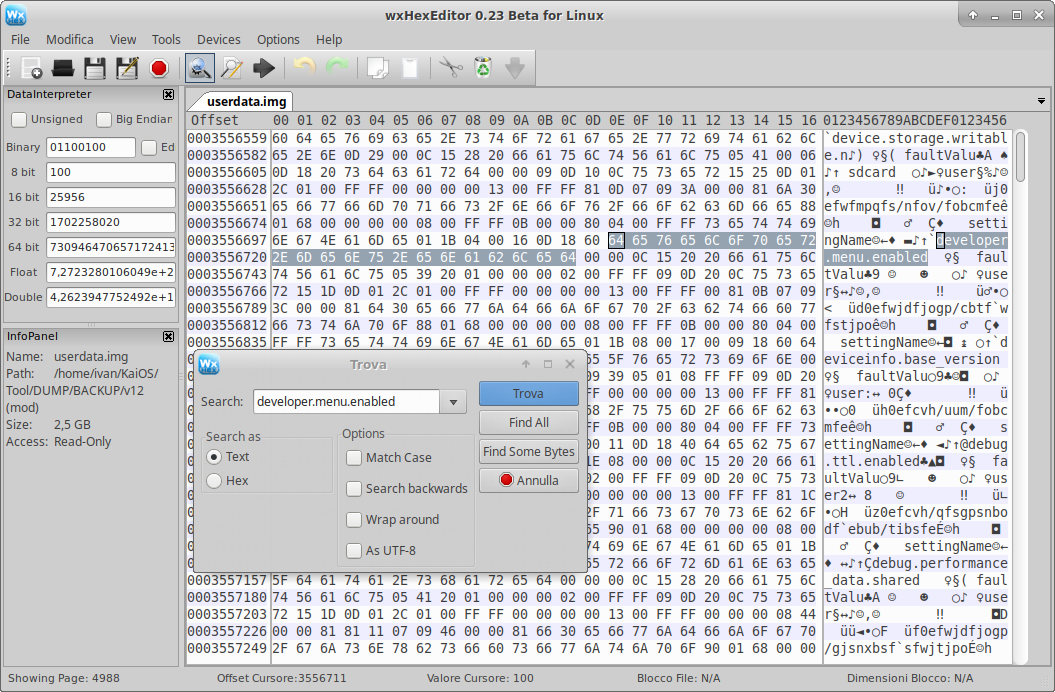
3. Find the closest faultValu string fragment next to it;
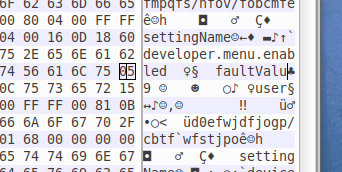
4. Measure exactly 8 bytes from that last u letter (the target byte should be 00) and change the value of that byte from 00 to 01.
Yes, we change a single bit in the huge image that weighs over 1GB, and after the device reboot the developer menu appears where it should: in the Settings - Device - Developer. You get both rooted ADB and DevTools access.
5. "Save as", in this way we 'll create a backup copy of our file without modify the original.
Enable ADB on the data partition
To be able to use ADB on your device there are two methods. The easiest is to patch the firmware directly (a fundamental partition, different from the userdata one), this is the topic of another guide:
The availability of ADB depends on its presence inside the boot partition (containing the drivers). Anyway, if you prefer to continue working on the data partition, this guide is for you.
Now that we have enabled the Developer menu in Settings, we have to enable the adbkey on the partition. Add the /home/.android/adbkey.pub file from your PC to /data/misc/adb/adb_keys in this way:
1. Mount the custom userdata.img and use root privileges to navigate/edit the file, for example:
mkdir /MOUNTPOINT
mount -o loop /LOCATION/userdata.img /MOUNTPOINT
where LOCATION is the folder containing the userdata.img file and MOUNTPOINT is the folder where you have mounted it, for example /mnt/img
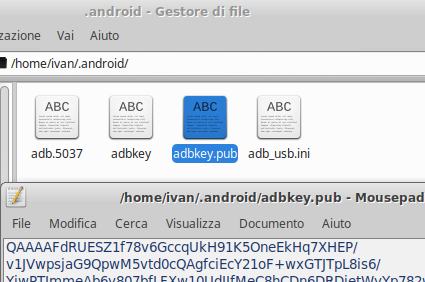
2. Copy the adb-publick-key on /data/misc/adb/adb_keys using this command:
cd ~/.android
cp -R adbkey.pub /MOUNTPOINT/misc/adb/adb_keys
3. Unmount the userdata.img file with the command umount /MOUNTPOINT/
Now your custom userdata.img file is ready to be flashed. This method is the safest way that does not stop the updates, however if you find it difficult try to patch the firmware using a backup boot.img that you can flash again in the notification of updates.
(source)Re-flash the data partition
Our custom data partition is ready to make the app sideload. Using EDL.PY and the loader for your device (for example your-firehose-x0000b.mbn):
To erase the partition, supply the -e [partname] option:
python3 edl.py -loader your-firehose-x0000b.mbn -e userdata
To flash a new partition image, supply the -w [partname] [filename] option:
python3 edl.py -loader your-firehose-x0000b.mbn -w userdata userdata.img
